How to Recognize and Avoid Spam Emails & Phishing Scams
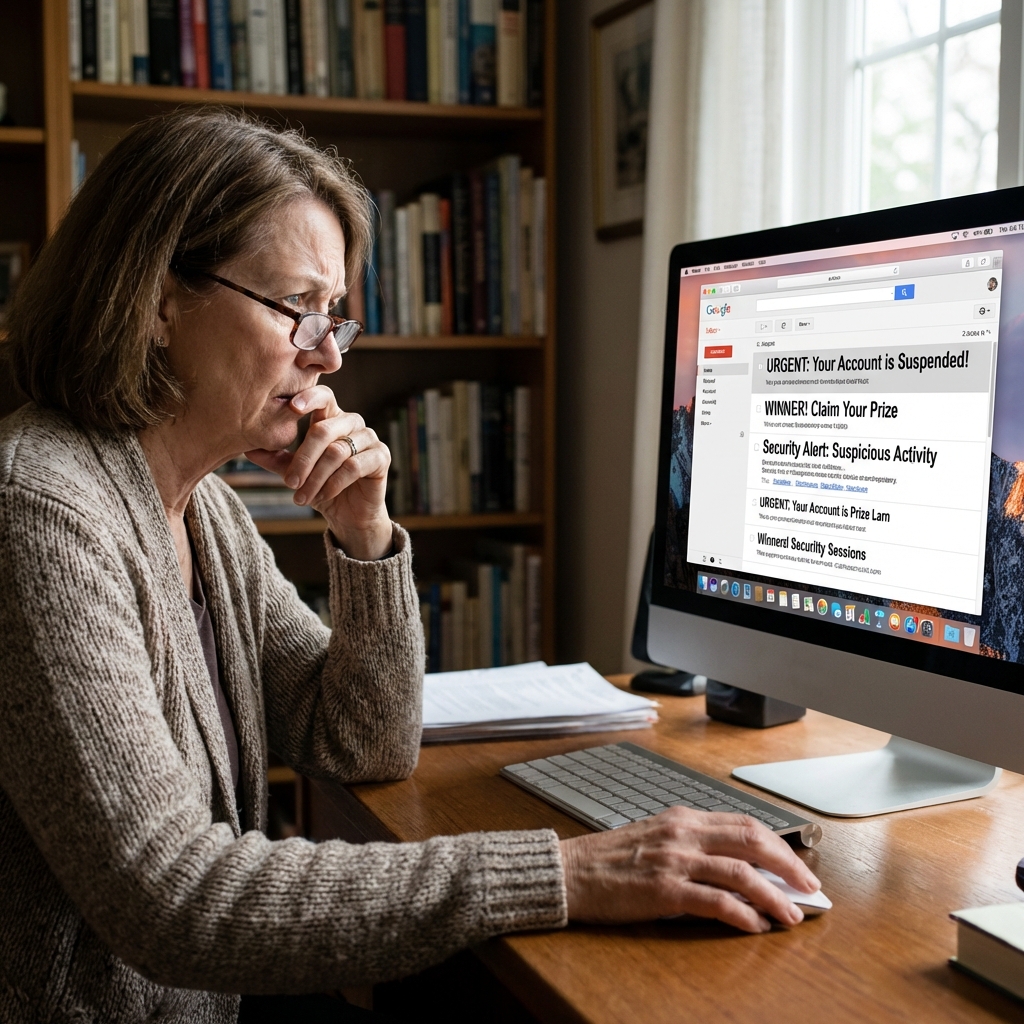
Learn the warning signs of dangerous emails and protect yourself from cyber criminals who try to steal your personal information through deceptive messages.
Understanding the Threat
Every day, millions of Americans receive fraudulent emails designed to trick them into revealing sensitive information like passwords, credit card numbers, and Social Security numbers. These attacks, known as phishing scams, have become increasingly sophisticated and can fool even the most tech-savvy individuals. As a home user, understanding how to identify these threats is your first line of defense against cybercriminals.
Phishing emails often impersonate trusted organizations such as banks, government agencies, popular retailers, or even friends and family members. They create a sense of urgency to pressure you into acting quickly without thinking critically about the request.
Warning Signs of a Phishing Email
Learning to spot the red flags in suspicious emails can save you from becoming a victim. Here are the most common indicators that an email may be a scam:
- Urgent or Threatening Language: Messages claiming your account will be closed, you owe money, or legal action will be taken unless you act immediately are almost always scams.
- Generic Greetings: Legitimate companies usually address you by name. Emails starting with "Dear Customer" or "Dear User" are often fraudulent.
- Suspicious Sender Addresses: Check the actual email address, not just the display name. Scammers often use addresses that look similar to real companies but have slight misspellings.
- Poor Grammar and Spelling: Many phishing emails contain obvious errors because they're often created by non-native English speakers or rushed out in bulk.
- Unexpected Attachments: Never open attachments from unknown senders. They may contain malware that can infect your computer.
- Requests for Personal Information: Legitimate organizations will never ask for passwords, Social Security numbers, or full credit card details via email.
Pro Tip: When in doubt, don't click any links in the email. Instead, open your web browser and manually type the official website address to access your account.
How to Protect Yourself
Taking proactive steps to protect yourself from phishing attacks is essential in today's digital world. Here's what you can do:
- Hover Over Links: Before clicking any link, hover your mouse over it to preview the actual URL. If it looks suspicious or doesn't match the supposed sender, don't click it.
- Enable Two-Factor Authentication: Add an extra layer of security to your important accounts. Even if someone steals your password, they won't be able to access your account without the second verification step.
- Keep Software Updated: Regularly update your operating system, web browser, and antivirus software to protect against the latest threats.
- Use Spam Filters: Most email providers have built-in spam filters. Make sure yours is enabled and set to a reasonable sensitivity level.
- Verify Suspicious Requests: If you receive an unexpected email from a company or person you know, call them directly using a phone number from their official website not from the email.
What to Do If You've Been Scammed
If you believe you've fallen victim to a phishing scam, take immediate action:
- Change your passwords for any accounts that may have been compromised
- Contact your bank immediately if you shared financial information
- Run a full antivirus scan on your computer
- Report the phishing attempt to the FTC at reportfraud.ftc.gov
- Monitor your credit reports for any unauthorized activity
Remember, staying vigilant is your best defense. If something feels off about an email, trust your instincts and verify before taking action. CyberShieldCare is always here to help you navigate these challenges safely.

